-
In Deployment config (Docs here)
Unfortunately it’s currently not possible to sync resources with pem files across your instances via Source Control - a workaround here is to set this up in your instances and set the resource up as follows.
Also any certs included in your deployment config would then essentially be trusted for all the more general HTTPS traffic coming to and from the container (whether that's other resource queries, connecting to a server with custom certs for source control, etc.)
-
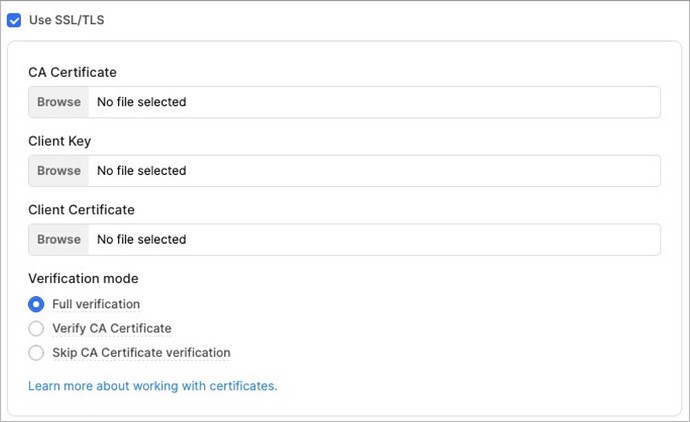
Tick use SSL/TLS in your resource but don’t upload a CA Certificate:
-
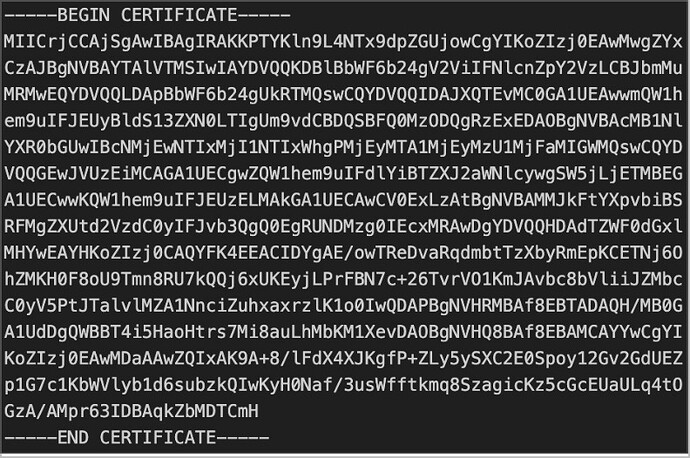
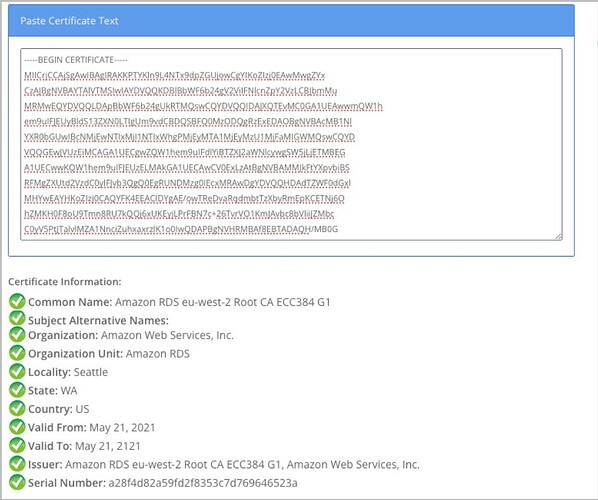
Get your PEM file from your resource provider. For AWS RDS resources, download the regional certificate bundle (AWS uses certificates from trusted CAs like Amazon Trust Services). Your certificate (PEM file) will look something like this
-
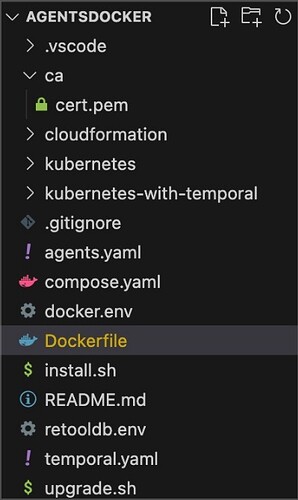
Create a folder in your deployment (in root) called ca
-
Create a pem file in folder ca and copy paste your certificate into it
-
Create a pem file in folder ca and copy paste your certificate into it
-
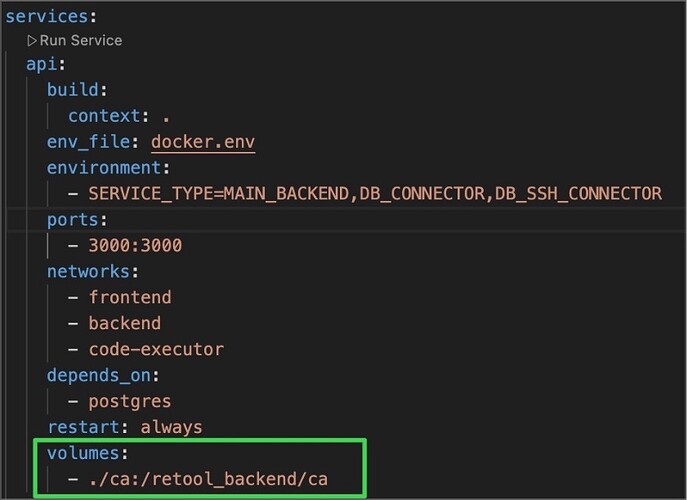
Mount the volume in your api service in your compose.yaml file
-
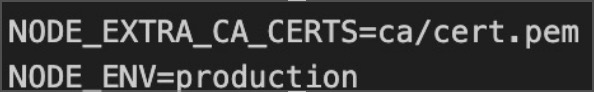
Tell your Node.js that it can trust certificates the server provides by setting the following env vars in your docker.env
Some other tips
-
You can decode your PEM certificate with a certificate decoder
-
The functionality that was previously handled by a separate db-connector service is now included in the api service. The api service handles both the main backend and the database connector roles. If your deployment runs a db-connector separately mount your certificate in the service as outlined in our docs
-
Your self hosted instance will automatically be set up with a global-bundle.pem which ensures SSL for your main storage DB that holds all your user, permission, page_saves, etc. records of your instance. You can see this by exec’ing into your api container and running ls certs.
Further Reading
- Community post on Set Retool on-prem to connect to External API with SSL/TLS
- Different applications don't share a universal certificate trust store—each technology (OpenSSL, Java, Node.js, etc.) maintains its own list of trusted CAs in different locations, which is why you need to configure certificates specifically for the technology you're using. Retool builds it’s image with Debian as base image (see here)