Hey! There are a few threads out there requesting a user API - here are two that I know of from the feature request section (one, two). They don't specify a user invite API but that has been requested elsewhere as well. We have a couple of internal tickets for tracking the requests and I've linked this thread to them so we can pass it along if they're included.
Thanks for posting your thoughts on a workaround here @bradlymathews!
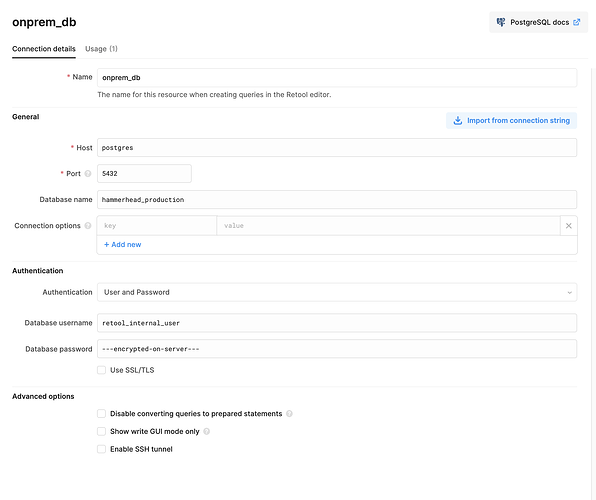
Also, to answer the question about how to do it on self-hosted. You can configure a Postgres resource to hit the storage database for your instance (this is separate from Retool Database) using the same credentials that are in your instance's environment variables.
The default setup would look something like this:
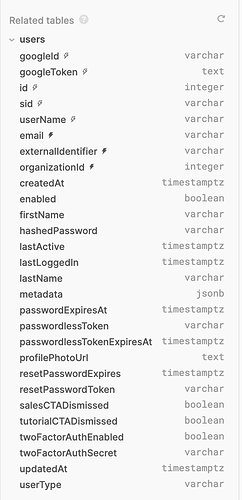
There's a users table in the database that should have the information you need: